Securing Your Crypto Wallets: Don’t Let Hackers Ruin Your Day
Look, let’s cut the crap. You’ve got crypto. You’re probably thrilled about it. But are you actually keeping it safe? Most people aren’t. They treat their digital gold like it’s Monopoly money, and guess what? Scammers and hackers are rubbing their hands together, just waiting to snatch it all up. This isn’t some futuristic movie; these threats are real, they’re happening right now, and they’re getting smarter.

Source : phishfort.com
Think about it. Your crypto lives in a wallet. That wallet is basically a digital vault. But unlike Fort Knox, there’s no armed guard. It’s just you, your passwords, and a bunch of code. And that code, well, it can be pretty complex. Keeping it all locked down? That’s the name of the game. We’re talking about protecting your digital assets from a whole slew of nasty characters who’d love nothing more than to empty your account faster than you can say “To the moon!
The New Era of Crypto Crime
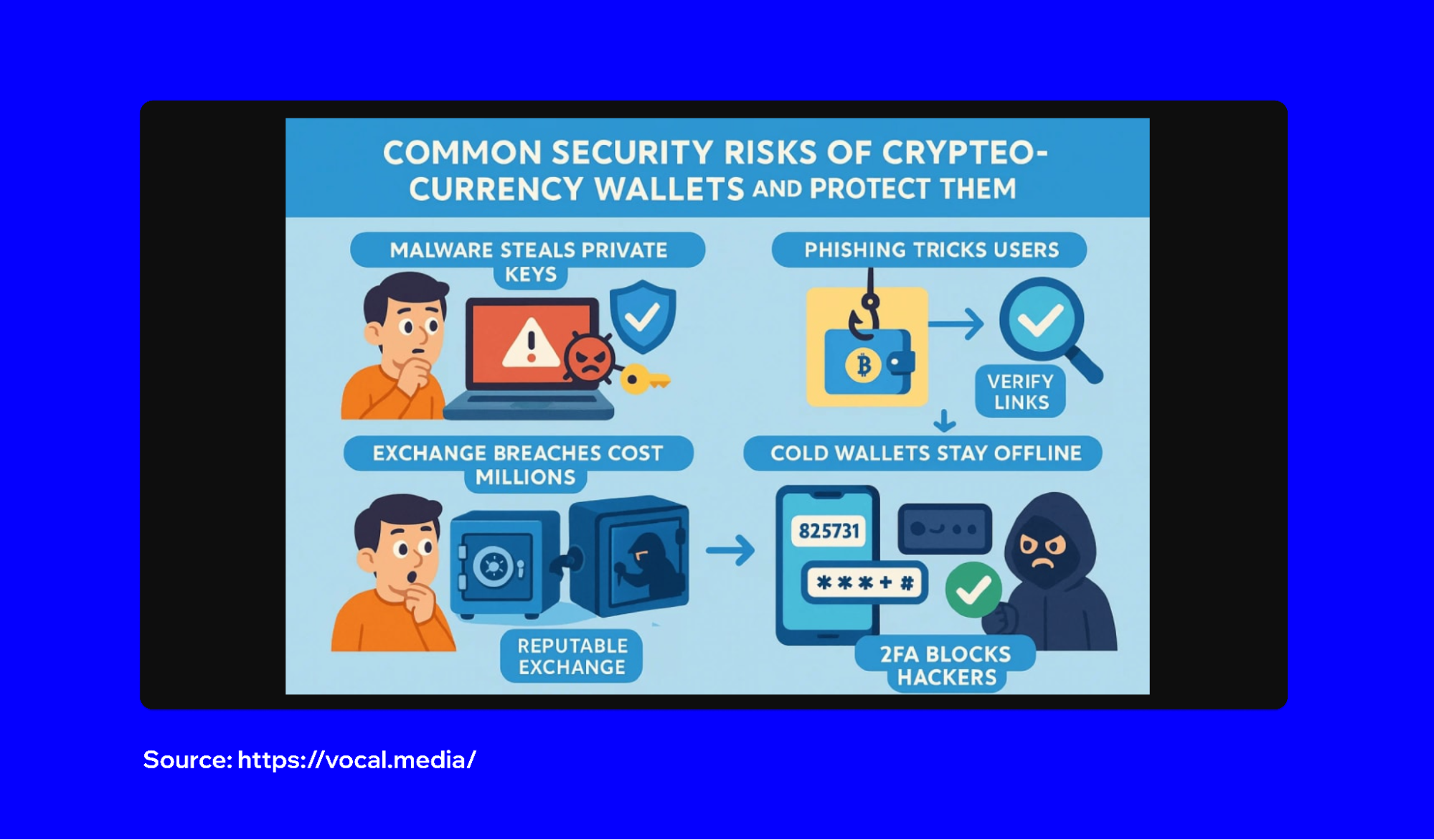
Gone are the days of simple password guessing. These guys are sophisticated. They’re using AI to craft convincing phishing emails, developing malware that can swipe your private keys right off your computer, and even ruing elaborate scams that trick you into sending them your coins yourself. It’s a full-blown war out there, and your wallet is the battlefield.
This isn’t just about losing money. It’s about losing your financial future, your hard-earned savings, and a ton of peace of mind. You pour your heart and soul into your investments, right? Then you gotta put that same energy into keeping your crypto safe. No excuses. No shortcuts.
Hot Wallets vs. Cold Wallets: The Big Debate
Alright, let’s get down to brass tacks. You’ve heard of hot wallets and cold wallets, yeah? Let’s break ’em down, no jargon, just the straight dope.
A hot wallet is basically any wallet coected to the internet. Think exchange wallets (like Coinbase or Binance) or mobile apps on your phone. They’re super convenient, right? Need to trade fast? Boom, it’s right there. But here’s the kicker: convenience comes with risk. Because they’re online, they’re sitting ducks for hackers. It’s like leaving your front door unlocked with a big sign that says “Free Cash Inside!” Not smart.
Then you’ve got cold wallets. These bad boys are offline. We’re talking hardware wallets (like Ledger or Trezor) that look like fancy USB drives, or even paper wallets (though those are way more fiddly). Because they aren’t coected to the internet, they’re incredibly secure. Hackers can’t get to them remotely. It’s like burying your treasure in the backyard – way harder to find.

Source : vocal.media
So, what’s the verdict? If you’re trading crypto daily, a hot wallet might be part of your setup for quick access. But for serious holdings, the ones you plan to HODL? You absolutely, positively need a cold storage solution. Don’t be a hero. Don’t be lazy. Move your long-term stash offline.
The Danger Zone: Exchange Wallets
Let’s talk exchanges for a sec. Places like Binance, Coinbase, Kraken – they’re super popular. And yeah, they make it easy to buy and sell. But here’s the thing: when your crypto is on an exchange, it’s not really yours. It’s in their wallet. They hold the private keys. Think of it like parking your car in a valet lot. The valet has the keys, not you.
This is a massive risk. Exchanges get hacked. It happens. And when it does, people lose everything. Remember Mt. Gox? That was a disaster. So, while using an exchange is fine for trading, you should never keep large amounts of crypto there long-term. Move it to a wallet you control. Your keys, your crypto. That’s the motto.
Hardware Wallets: Your Digital Armored Car
If you’re serious about crypto security, a hardware wallet is non-negotiable. These devices are designed from the ground up to keep your private keys offline, isolated from your internet-coected computer or phone. When you make a transaction, it’s signed on the device itself, so your keys never touch the web.
Buying one is like getting an armored car for your digital money. Sure, it costs a bit upfront (usually $50-$200), but what’s that compared to potentially losing thousands or even millions? Look at brands like Ledger and Trezor. Do your research, figure out which one fits your needs, and get one. It’s an essential security investment.
Seed Phrases: The Master Key (Guard It Closely!)
Okay, this is HUGE. When you set up most non-custodial wallets (the ones where you control the keys), you’ll get a seed phrase. It’s usually a list of 12 or 24 random words. This phrase is the master key to your entire crypto fortune.
If you lose your wallet device, or your phone gets wiped, this seed phrase is what lets you recover all your funds. Simple as that. But here’s the terrifying part: if anyone else gets their hands on your seed phrase, they can steal everything. They can literally restore your wallet onto their own device and drain it dry.
So, what do you do? First, write it down. Don’t just screenshot it. Don’t save it in a text file. Write it down on paper. Then, store that paper somewhere incredibly safe. Think a fireproof safe, a safety deposit box, or even multiple secure locations. Never, ever store it digitally. Never share it. Anyone asking for your seed phrase is trying to rob you. Period. Seriously, protect your seed phrase like your life depends on it, because your financial life probably does.
Phishing and Social Engineering: The Art of the Scam
These scammers are smooth. They know how to play on your greed and your fear. Phishing isn’t just about fake emails anymore. It’s personalized texts, fake social media profiles, even direct messages designed to look like they’re from a legitimate project or a trusted friend.
They might offer you a “free airdrop” (just send a tiny bit of crypto to cover gas fees!), tell you your account is “under review” (click this link to verify!), or claim you’ve “won a prize” (just coect your wallet to claim!). All of it is designed to get you to either:
- Click a malicious link.
- Download malware.
- Send them your crypto directly.
- Reveal your private keys or seed phrase.
The golden rule? If it sounds too good to be true, it absolutely is. Always, always, always verify the source. Double-check URLs. Never click on links in unsolicited messages. Be paranoid. It’s better to be safe than broke.
Fake Wallets and Malicious Apps
This one’s a real nasty trick. Hackers create fake versions of popular crypto wallets and list them in app stores. They look identical, but behind the scenes, they’re stealing every bit of information you put into them. They might even clone popular websites, so when you try to log in, you’re feeding your details straight to the bad guys.

Source : stellarcyber.ai
How do you avoid this? Stick to official sources. Only download wallet apps from the official websites of the developers. For exchanges, always type the URL directly into your browser or use a bookmark you created yourself. Don’t trust search engine results for crypto sites. They can be manipulated.
The Dangers of Malware
Malware is the silent killer of crypto fortunes. It can be hidden in seemingly iocent downloads – a free game, a PDF document, a software update. Once installed, it can lurk in the background, watching everything you do.
Keyloggers can record every keystroke, meaning they’ll grab your passwords and seed phrases. Screen scrapers can capture sensitive information displayed on your screen. Some malware even directly targets cryptocurrency wallet files or transaction data. Your best defense? Keep your operating system and antivirus software up to date. Be incredibly selective about what you download and install, especially on any device you use for crypto. Strong antivirus software is a must.
Protecting Against SIM Swapping and SMS Interception
Ever think about how much of your online life is tied to your phone number? For 2FA (two-factor authentication), account recovery, and more? Yeah, criminals know that too. A SIM swap attack is where a hacker tricks your mobile carrier into transferring your phone number to a SIM card they control. Suddenly, all your texts, including those one-time login codes, go straight to them.
This allows them to bypass 2FA on exchanges and other platforms. It’s terrifyingly effective. The best defense? Use authenticator apps (like Google Authenticator or Authy) instead of SMS for 2FA whenever possible. These codes aren’t sent over the network, making them much harder to intercept. Also, add a PIN or special password to your mobile carrier account. This makes it harder for them to trick the carrier into a SIM swap. It’s a crucial security layer.
The Rise of Deeper Scams: Pig Butchering
This one’s particularly insidious. A “pig butchering” scam starts with a seemingly random message from a stranger on social media or a dating app. They build a relationship with you over weeks or months, gaining your trust. Then, they “butcher the pig” by convincing you to invest in fake crypto platforms, often showing you fake profits before asking you to deposit more funds – which they then steal.
It’s psychological warfare, plain and simple. They exploit loneliness and trust. The takeaway here is simple: be incredibly wary of romantic advances or new friendships that quickly turn to unsolicited investment advice, especially in crypto. Be skeptical of online relationships that push financial opportunities.
Best Practices for Bulletproof Wallet Security
Okay, we’ve covered a lot of ground. Let’s boil it down to the absolute must-dos. These aren’t suggestions; they’re essential habits.
1. Use a Hardware Wallet for Significant Holdings: I can’t stress this enough. If you have more than a few hundred bucks in crypto, get a hardware wallet. Keep your long-term investments offline and secure.
2. Secure Your Seed Phrase Like Gold: Write it down. Store it offline. Never share it. Treat it like the master key it is. A lost or stolen seed phrase means a lost or stolen crypto portfolio. It’s the single most important recovery tool.
3. Enable All Available Security Features: Use strong, unique passwords for exchanges and wallets. Enable 2FA using an authenticator app, not SMS. Look for anti-phishing codes in emails from exchanges. Add PINs to your mobile service. Every little bit helps.
4. Be Suspicious of Everything Online: Got an email about your account? A DM about a hot new coin? A link from a “friend”? Pause. Think. Verify. Never click suspicious links or download unknown files.
Source : trustwallet.com
5. Keep Software Updated: Your operating system, your browser, your antivirus, your wallet software – keep it all updated. Patches often fix critical security vulnerabilities that hackers exploit. It’s a simple step that enhances overall protection.
6. Use Different Wallets for Different Purposes: Don’t put all your eggs in one basket. Have a “hot” wallet for small, frequent transactions and a “cold” wallet for your main stash. This limits your exposure if one wallet is compromised. Think of it as diversifying your security.
7. Beware of Public Wi-Fi: Never access your crypto wallets or exchanges on public Wi-Fi networks. These are notoriously insecure and easy for hackers to monitor. Stick to your secure home network or use a VPN if you absolutely must coect remotely. Public Wi-Fi is a hacker’s playground.
8. Educate Yourself Continuously: The crypto space moves fast, and so do the scams. Stay informed about the latest threats. Read security blogs, follow reputable crypto security experts on social media, and learn about new attack vectors.
When to Seek Professional Help
Sometimes, despite your best efforts, things go wrong. If you suspect you’ve been compromised, or if you’re just overwhelmed by the complexity of securing your assets, don’t hesitate to reach out for help. There are cybersecurity professionals who specialize in crypto. They can help you recover funds if possible, secure your remaining assets, and put robust security measures in place. It might cost money, but it’s often cheaper than losing everything.
Conclusion: Your Crypto, Your Responsibility
Keeping your crypto safe isn’t just a good idea; it’s your job. The technology is complex, and the threats are real and evolving. But by understanding the risks and implementing strong security practices – especially using hardware wallets and safeguarding your seed phrase – you can dramatically reduce your chances of becoming another victim.
Don’t wait until it’s too late. Start securing your digital assets today. The peace of mind is worth more than any Bitcoin price surge. Remember, security is an ongoing process, not a one-time fix.
Frequently Asked Questions
-
Can the FBI track a Bitcoin wallet?
Yeah, the FBI can definitely track Bitcoin wallets, but it’s not like they’ve got a magic tracker. They use blockchain analysis tools – essentially, they follow the money trail on the public ledger. If a wallet is linked to an exchange where they can get user information, or if it’s involved in a known criminal activity, they can often trace transactions back to individuals. It’s more about data analysis and coecting the dots than instant tracking. So, while your wallet address itself is pseudonymous, it’s not entirely anonymous, especially if law enforcement gets involved. Chain analysis is key for them.
-
What's the difference between a custodial and non-custodial wallet?
Great question! Think of it like this: a custodial wallet is like a bank. You deposit your crypto, and they hold it for you. They manage the private keys. Examples are exchange wallets like on Coinbase or Binance. Convenient, but you don’t truly control your keys. A non-custodial wallet, on the other hand, means YOU hold the keys. You’re in complete control. Examples are hardware wallets like Ledger or software wallets like MetaMask. Your seed phrase is your responsibility. It’s your crypto, your keys, your rules – but also your risk if you mess up.
-
How often should I back up my crypto wallet?
It’s not really about frequency like backing up photos; it’s about securing your seed phrase. For most non-custodial wallets, you only need to back up your seed phrase once when you create the wallet. After that, the critical thing is to ensure that physical backup is safe, secure, and accessible only to you. You don’t ‘back up’ the wallet daily. You ensure your recovery mechanism (the seed phrase) is protected. If you’re using a custodial wallet on an exchange, they handle the backups, but again, that’s why you don’t keep large amounts there.
-
Is it safe to use a VPN with my crypto wallet?
Using a good VPN can add a layer of security, especially if you’re accessing your wallets on potentially untrusted networks like public Wi-Fi. It encrypts your internet traffic, making it harder for snoops on the same network to intercept your data. However, it’s NOT a magic bullet. It won’t protect you from phishing scams, malware on your device, or if you accidentally send funds to the wrong address. Think of it as good hygiene, not a complete immune system. It enhances your privacy, but diligence is still key.
-
What are the biggest mistakes people make securing their crypto?
Oh man, where do I even start? The biggest one? Being lazy with the seed phrase. Seriously, people write it on sticky notes, save it in cloud storage, or email it to themselves. Huge mistake. Another massive one is leaving too much crypto on exchanges – that’s basically asking for trouble when they inevitably get hacked. People also fall for phishing scams way too easily, clicking links or giving up info they shouldn’t. Lastly, not using a hardware wallet for anything more than pocket change. It’s like leaving your house keys under the mat. Basic security fail.
